Recently, a friend sent me the following E-mail from Senator Barbara Boxer (D) California...
Dear Friend:
We recently learned of a major data breach at the Office of Personnel Management (OPM) that may have put the personal information of millions of current and former federal employees at risk.
AND IF THAT WASN’T ENOUGH…by dStringer
Safety Tips if Your “Traveling Companion” Is Your Lap Top…by DStringer

Hitting the road with your computer opens the doors to a whole world of potential security problems, both physical and software-based, but don't worry. They're all manageable. Remember, the weakest link in your security will usually be you—as long as you don't put yourself, your computer, or its data at undue risk, you should be just fine even if you have to work from a library or a coffee shop, or connect to whatever Wi-Fi you find to get some work done.
PRIVATE EYES?? WHO CAN REALLY SEE YOUR TEXTS?? by DStringer

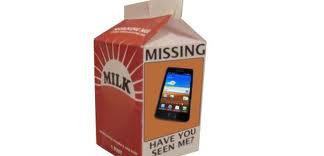
They’re everywhere: in cars, shopping malls, and restaurants, even at family and professional sporting events. They are so common place these days, I'm not sure I know anyone who doesn't own one...the "attached at the hip" CELL PHONE!! Have you noticed, though, how often a wireless phone isn’t being used to actually talk to another person.
SECURE IT WELL…PROTECT YOUR CELL by dStringer
UNLOCKING THE MYSTERIES OF THE “CLOUD” by DStringer

"Cloud Computing" is definitely the buzzword "De Jour"...but there are very few of us who really understand what this is and how it works. So here is a little "Cloud 101" to hopefully allow a little better understanding of this phenomenon.
"Cloud Computing" means that instead of all the computer hardware and software you're using sitting on your desktop, or somewhere inside your company's network, it's provided for you as a service by another company and accessed over the Internet, usually in a completely seamless way.
HUMANS ARE THE WEAKEST LINK…by dstringer
IS DATA BACK-UP PART OF YOUR “DISASTER” KIT?? by dorothy stringer

In the news recently, it seems there have been more natural disaster phenomenons globally, occurring almost daily. Earthquakes, Tornadoes, Floods, Fires. We are all warned and drilled on the importance of preparing for and keeping a "disaster kit"...in our case in Southern California, it is known as an "Earthquake Kit". The essentials are packed in the kit.
THIS IS NO JOKE…by dorothy stringer

Identity theft, social engineering, phishing,...these are all terms that are part of our life, whether you are aware or not. We are so tied to our computer and the internet. And even if you are not technically savvy, the world around you is, and because of that, your security is tied in with the world.
“OH NO!!” AVOIDING THIS COMMON REACTION (or…Protecting Your PC From Lost Data) by dstringer
WHAT YOU DON’T KNOW CAN HURT YOU…by dstringer

For the chosen few in the world of "Geek" (I say that lovingly) their minds are imprinted with a keen sense of intricacies on all, or at least most aspects of Information Technology.
But for the general public, most of us understand very little about the world of I.T. And so, in the specific case of "cyber security", our lack of knowledge sets us up to be "sitting ducks.




You must be logged in to post a comment.